Telegram Bug Bounty Bot https://telegram.me/bug_bounty_channel History This bot adopted special for deploying to Herok...
Your Ads Here
Friday, 30 December 2016
Thursday, 29 December 2016
 Cloud pentesting
Computer Forensic
Cryptography
Distribution
Distro
Hacking
Linux
Parrot Security OS
Pentesting
Privacy/Anonimity
Reverse Engineering
Cloud pentesting
Computer Forensic
Cryptography
Distribution
Distro
Hacking
Linux
Parrot Security OS
Pentesting
Privacy/Anonimity
Reverse Engineering
Parrot Security 3.3 - Security GNU/Linux distribution designed with cloud pentesting and IoT security in mind
Security GNU/Linux distribution designed with cloud pentesting and IoT security in mind. It includes a full portable laboratory for security...
Wednesday, 28 December 2016
 Aircrack-ng
Capture
DNS
Fluxion
GREP
Kali
Kali Linux
LINSET
Linux
MDK3
MITM
Network
Responder
WEP/WPA/WPS
Wifi
Wireless
WPA
WPA2
Aircrack-ng
Capture
DNS
Fluxion
GREP
Kali
Kali Linux
LINSET
Linux
MDK3
MITM
Network
Responder
WEP/WPA/WPS
Wifi
Wireless
WPA
WPA2
Fluxion 0.23 - WPA/WPA2 Security Hacked Without Brute Force
Fluxion is a remake of linset by vk496 with (hopefully) less bugs and more functionality. It's compatible with the latest release...
Tuesday, 27 December 2016
Lobotomy - Android Reverse Engineering
Lobotomy is a command line based Android reverse engineering tool. What is in the repo, is currently in development. You should assume not...
Monday, 26 December 2016
 BSD
Discover
Heartbleed
IPv6
Kali
LDAP
Linux
MD5
OpenSSL
PostgreSQL
Protocols
RDP
SSL/TLS
sslscan
STARTTLS
TLS
TOR
Windows
BSD
Discover
Heartbleed
IPv6
Kali
LDAP
Linux
MD5
OpenSSL
PostgreSQL
Protocols
RDP
SSL/TLS
sslscan
STARTTLS
TLS
TOR
Windows
sslscan - tests SSL/TLS enabled services to discover supported cipher suites
This is a fork of ioerror's version of sslscan (the original readme of which is included below). Changes are as follows: Highlight ...
Sunday, 25 December 2016
Raptor WAF v0.04 - Web Application Firewall using DFA
Raptor WAF is a simple web application firewall made in C, using KISS principle , to make poll use select() function, is not better than e...
Saturday, 24 December 2016
 Aircrack-ng
Aireplay-ng
Airodump-ng
Android
Cracking
Firmware
Hijacker
MDK3
NetHunter
Nexus
Reaver
Wep
Wifi
Wireless
WPA
WPS
Aircrack-ng
Aireplay-ng
Airodump-ng
Android
Cracking
Firmware
Hijacker
MDK3
NetHunter
Nexus
Reaver
Wep
Wifi
Wireless
WPA
WPS
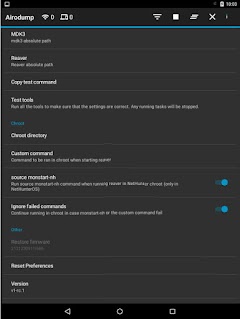
Hijacker - Aircrack, Airodump, Aireplay, MDK3 and Reaver GUI Application for Android
Hijacker is a Graphical User Interface for the wireless auditing tools airodump-ng, aireplay-ng and mdk3. It offers a simple and easy...
Friday, 23 December 2016
 Analysis
Linux
Mac
Malware
Malware Analysis Sandbox
Noriben
Python
Sysinternals
VirusTotal
Windows
Yara
Analysis
Linux
Mac
Malware
Malware Analysis Sandbox
Noriben
Python
Sysinternals
VirusTotal
Windows
Yara
Noriben - Portable, Simple, Malware Analysis Sandbox
Noriben is a Python-based script that works in conjunction with Sysinternals Procmon to automatically collect, analyze, and report on runtim...
Subscribe to:
Posts (Atom)







